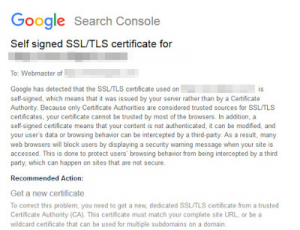
Google Search Console: a self-signed SSL/TLS certificate for a website

When the Google tool – Google Search Console (GSC) is used, we may receive a message entitled: „Self-signed SSL/TLS certificate for the website (this is usually followed by the name of the website involved).
Obviously, you will not receive this kind of message if you don not use the Google Search Console tool. When can such a message be received? And is it really a mistake on our part? As it turns out, the answers to these questions is a bit more complicated. We are going to explain why below.
Table of Contents
Toggle1. SNI enabled.
SNI (Server Name Indication) is an extension to the SSL protocol, which allows you to install several SSL certificates on a single IP address without the necessity for a dedicated IP address. Such a solution has been introduced because the resources of IPv4 addresses are going slowly thin. When using the SNI, hosting companies may reduce the IPv4 addressing usage, and their customers can install numerous SSL certificates onto their domains. Unfortunately, this solution has some serious limitations e.g. for older operating systems and Internet browsers. Upon visiting a website that uses SNI and a SNI-based SSL certificate, a user who works with an older browser may be alerted that this page does not have a trusted certificate. Such an alert will be displayed regardless of whether or not an SSL certificate has properly been installed. The situation might be the same in case of the Google bot. The Googlebot obviously, enters our website and identifies with various browsers and operating systems, for example:
66.249.76.137 - - [08/Aug/2018:14:15:10 +0200] "GET xxxx HTTP/1.1" 200 17979 "-" "Mozilla/5.0 (Linux; Android 6.0.1; Nexus 5X Build/MMB29P) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2272.96 Mobile Safari/537.36 (compatible; Googlebot/2.1; +http://www.google.com/bot.html)"
66.249.66.159 - - [08/Aug/2018:06:41:46 +0200] "GET xxxx HTTP/1.1" 200 1006 "-" "Mozilla/5.0 AppleWebKit/537.36 (KHTML, like Gecko; compatible; Googlebot/2.1; +http://www.google.com/bot.html) Safari/537.36"
It is possible, then, that the Googlebot will enter our website will identifying as a browser or a system that does not support SNI, and as a result, we may receive a GSC alert about the the self-signed certificate. Although such situations are rather uncommon, they do unofrtunately take place. What to do then? First of all, do not panic – the best idea is to check if the SSL certificate was properly recognized by the earlier builds of given browsers. The SSLLabs’ tool can prove helpful in this procedure. It can be found on https://www.ssllabs.com/ssltest/index.html
If everything is alright, such a message can safely be ignored. Still, if we want to provide 100% compatibility of our SSL certificate with the browser or the operating system of our visitor, we must establish a dedicated (not shared) IP address for our domain or service. More information on the SNI technology may be found on Wikipedia: https://en.wikipedia.org/wiki/Server_Name_Indication
2. Transferring your website between two servers.
It is a very special case, but it reoccurs in case of receiving GSC alerts. It happens that we need to move our website or service from one server to another (regardless of whether or not we require a stronger unit or our hosting provider has run into problems). Moving your website uusually means that its IP address changes as well, an this kind of shift must be propagated by DNS systems. Although in most cases the introduced changes are visible pretty fast, there are cases in which they may become visible only after 24 hours, for instance. It is generally believed that the propagation of DNS changes may take somewhere between 48 and 72 hours. If, for some reason, we decided to remove our website from the previous server, there is a possibility that the Googlebot will hit the gap thus created. The result of this may be the GSC alert. Therefore, it is good practice to make sure that everything functions and is displayed properly after the website has been moved. This particularlyu means checking if the certificate is properly displayed in the browser. If, despite the move, we still encounter some SSL certificate-related issues, it is a good idea to check the configuration or, in some cases, to contact the technical assstance crew of your hosting provider.
3. An invalid or expired SSL certificate.
Much as this situation may appear unusual, it does happen quite frequently. Needless to say that each SSL certificate has its expiration date. Usually, it is around 30 to 90 days for trial SSL certificates, and one or two years for more standard cases. Each certificate purchased for the duration of one or two years, can be prolonged as early as 90 days before its expiry date. This does not, of course, mean that a certificate prolonged some 89 days before expiry date will be valid the 89 days shorter. When placing an order, when you choose the RENEWAL option, the 90 days period will automatically be added to your new SSL certificate no matter if you prolonged your certification two or eighty nine days before expiry date. It is worthwhile, therefore, to pay attention to the expiry time to prolong your certification service before it does actually expire, especially, given the fact that a notification about the upcoming expiry date is usually sent to you in advance. Apart from the GSC notification, an alert about the expired SSL certificate will be displayed to anyone who enters a website which has a certificate that is no longer valid. This may make a user decide to resign from visiting a website. A GSC may also appear when our SSL certificate has not been properly installed (for instance, when a server certificate appears) or there are proxy certificates missing. After receiving a message, it is a good idea to check if our certificate is properly recognized by browsers or run diagnostics using the aforementioned SSLLABS tool: https://www.ssllabs.com/ssltest/index.html
In each of the presented cases, having received a Google message, it is a good idea to check the SSL certificate on the website the message referred to. Thanks to this, we can uproot the errors that may lower the security of our website as well as negatively influence its rank in the Google search engine.
